Cloud Security & Compliance Solutions Perth
Control map
The cloud controls that reduce real operating risk
Security work is grouped around the controls that protect access, data, networks and compliance evidence.
Identity
MFA, least privilege, service accounts, access reviews and privileged access controls.
Network
Segmentation, private endpoints, firewall rules, ingress controls and secure connectivity.
Data
Encryption, backup policy, key management, retention and recovery testing.
Evidence
Logging, alerting, audit trails and compliance reporting for regulated environments.
Nano Solutions delivers cloud security and compliance solutions for Perth businesses, supporting SOC 2, ISO 27001, and Australian government security standards. We protect infrastructure across AWS, Azure, GCP, DigitalOcean, and hybrid/on-premises environments with defence-in-depth strategies.
Cloud Compliance Solutions
Navigating SOC 2, ISO 27001, Essential Eight, and Australian Privacy Principles compliance is complex. Nano Solutions provides end-to-end cloud compliance solutions — from gap assessment and control implementation to audit-ready evidence packages. We help Perth businesses and government agencies meet their regulatory obligations without disrupting operations.
Advanced Cloud Security Solutions
Safeguard Your Cloud Environment Against Evolving Threats
As businesses increasingly move to the cloud, securing cloud environments has become paramount. Nano Solutions' cloud security services provide comprehensive protection for your cloud infrastructure, applications, and data against sophisticated cyber threats.
Key Features of Our Cloud Security Services
- Cloud Infrastructure Security: We secure your cloud infrastructure with advanced security measures, including firewalls, intrusion detection, and prevention systems.
- Data Protection: Our services include encryption, access control, and data loss prevention strategies to protect your sensitive data in the cloud.
- Identity and Access Management (IAM): We implement IAM solutions to ensure only authorised users can access your cloud resources.
- Compliance and Governance: We help you navigate the complex landscape of cloud compliance, ensuring your cloud environment adheres to industry regulations and standards.
Why Choose Nano Solutions for your Cloud Security Needs?
Get Comprehensive Protection with Our Cloud Protection Services
We offer end-to-end cloud security solutions to protect every aspect of your cloud environment.
Team of Cloud Security Experts in Perth WA
Our team has extensive experience in cloud security, ensuring your cloud assets are in safe hands.
Our Customised Approach to Cloud Security
We understand that every business is unique. Our cloud security solutions are tailored to meet your specific needs and challenges.
Our Cloud Security Process
- Security Assessment & Audit: We evaluate your current cloud environment, identifying vulnerabilities, misconfigurations, and compliance gaps. The output is a detailed security posture report with risk-prioritised findings.
- Security Architecture Design: Based on the assessment, we design a defence-in-depth security architecture tailored to your platform (AWS, Azure, GCP, DigitalOcean, or hybrid/on-premises), business requirements, and compliance obligations.
- Implementation & Hardening: We deploy security controls including network segmentation, encryption, IAM policies, logging, and monitoring. Each control is tested and validated before moving to the next.
- Compliance Configuration: We configure your environment to meet specific compliance frameworks — SOC 2, ISO 27001, Essential Eight, or WA Government security standards — with automated compliance checking.
- Penetration Testing: Authorised security testing simulates real-world attack scenarios to validate your defences. We provide a detailed report with remediation guidance for any findings.
- Ongoing Monitoring & Response: Continuous security monitoring, threat detection, and incident response procedures keep your environment protected as threats evolve.
Compliance Frameworks We Support
- Australian Government ISM: Information Security Manual compliance for government agencies and contractors handling sensitive data.
- Essential Eight: The Australian Cyber Security Centre's Essential Eight Maturity Model — we assess your current maturity level and implement controls to reach your target level.
- SOC 2 Type II: Service Organisation Control reports for businesses that handle customer data, covering security, availability, processing integrity, confidentiality, and privacy.
- ISO 27001: International information security management system certification preparation, including policy development, risk assessment, and control implementation.
- PCI DSS: Payment Card Industry Data Security Standard compliance for businesses that process, store, or transmit cardholder data.
Cloud Infrastructure We Harden
- Multi-account AWS / Azure / GCP environments: Organisation-level security policies, account isolation, centralised logging with CloudTrail or Azure Monitor, and guardrail enforcement via SCPs or Azure Policy.
- Hybrid and on-premises infrastructure: Site-to-site VPN, private endpoints, firewall rules, and identity federation between on-premises Active Directory and cloud IAM.
- Container and serverless platforms: Image scanning, runtime protection, least-privilege execution roles, and network policy for Kubernetes, ECS, and Lambda workloads.
- Data sovereignty configurations: Region-locked deployments, encryption key management with customer-managed keys, and data residency controls for Australian regulatory requirements.
- WA Government environments: As a CUAICTS2021 panel supplier (Contractor #225), we configure cloud infrastructure to ISM and Essential Eight standards with streamlined procurement.
Cloud Platforms We Secure
- Amazon Web Services (AWS): IAM policies, VPC security, GuardDuty, Security Hub, CloudTrail, Config rules, and WAF configuration.
- Microsoft Azure: Azure AD, Network Security Groups, Microsoft Defender for Cloud, Azure Sentinel, Key Vault, and Conditional Access policies.
- Google Cloud Platform (GCP): Cloud IAM, VPC Service Controls, Security Command Center, Cloud Armor, and organisation policies.
- DigitalOcean: Account security, networking, firewall rules, managed database access, Spaces configuration, Kubernetes hardening, monitoring, and backup controls.
- Multi-Cloud, Private Cloud & Hybrid: Unified security policies across multiple cloud providers, private cloud, and on-premises infrastructure, with centralised monitoring and incident response.
Typical Investment
Cloud security engagements vary based on scope and ongoing needs:
- Security Audits: From $5,000 for a focused assessment of a single cloud environment to $25,000+ for comprehensive multi-cloud security audits with penetration testing.
- Managed Security: From $1,500 per month for ongoing security monitoring, patch management, and incident response for small to mid-sized cloud environments.
Key factors that influence cost:
- Number of cloud accounts and environments
- Compliance framework requirements (SOC 2, ISO 27001, Essential Eight)
- Number of applications and services to protect
- Existing security maturity and gap remediation scope
- Incident response and monitoring requirements
Every engagement begins with a free security consultation where we assess your current posture and recommend a tailored approach.
Book a free security consultation to discuss your cloud security needs.
Indicative Pricing
Scope and pricing confirmed after a free consultation. All prices AUD, exclude GST.
Security Audit
From $5K
Single cloud environment
- IAM + network review
- Compliance gap analysis
- Risk-prioritised report
- Remediation roadmap
Hardening
From $15K
Audit + implementation
- Multi-account hardening
- Essential Eight or ISO 27001
- Penetration testing
- 4–8 week engagement
Managed Security
From $1,500/mo
Continuous protection
- 24/7 monitoring + alerting
- Patch management
- Incident response
- Quarterly posture review
Frequently Asked Questions
What cloud security services does Nano Solutions offer?
Nano Solutions offers a comprehensive range of cloud security services, including Identity and Access Management (IAM), data encryption, threat detection and response, compliance management, and multi-factor authentication (MFA). We also conduct regular vulnerability assessments and provide continuous monitoring.
How can Nano Solutions' cloud security solutions protect my business data?
Our cloud security solutions safeguard your business data through advanced encryption, access controls, and continuous monitoring. By identifying and mitigating risks in real-time, we ensure that sensitive data remains secure whether in storage, transit, or during processing.
What makes Nano Solutions a leading cloud security company in Australia?
Nano Solutions stands out as a leading cloud security provider due to our deep expertise, commitment to customisation, and focus on regulatory compliance. Our team leverages cutting-edge technology and industry best practices with over 20 years of experience.
How does Nano Solutions ensure compliance in cloud environments?
We stay up-to-date with relevant regulations, including GDPR, HIPAA, and the Australian Privacy Principles, ensuring that your cloud infrastructure complies with industry standards. We perform regular audits, implement necessary security controls, and provide comprehensive compliance reporting.
What is Identity and Access Management (IAM) and why is it important for cloud security?
Identity and Access Management (IAM) controls who can access your cloud resources and what actions they can perform. IAM is essential for cloud security, as it reduces the risk of unauthorised access. We implement IAM policies, including multi-factor authentication and role-based access controls.
How does Nano Solutions handle data encryption in the cloud?
Nano Solutions uses advanced encryption protocols to secure your data both at rest and in transit. We implement end-to-end encryption strategies and manage encryption keys to ensure only authorised users can access sensitive information.
What types of threats can Nano Solutions' cloud security services protect against?
Our cloud security services protect against a range of threats, including data breaches, malware, ransomware, denial-of-service (DoS) attacks, and insider threats. Our proactive approach includes continuous monitoring and threat intelligence to detect and address vulnerabilities.
What industries can benefit most from Nano Solutions' cloud security expertise?
Industries such as healthcare, finance, e-commerce, education, and government benefit greatly from our cloud security expertise. Our experience with regulatory requirements and industry-specific challenges allows us to develop targeted cloud security strategies.
How does Nano Solutions stay updated with evolving cloud security threats?
Our team continually monitors the latest cloud security trends and threat intelligence. We undergo regular training and certifications, and utilise advanced threat detection tools and global security networks to ensure we provide the most current and effective security strategies.
How much do cloud security services cost in Perth?
Cloud security audits typically start from $5,000 for a comprehensive assessment. Ongoing managed security services start from $1,500 per month, covering continuous monitoring, threat detection, and incident response. The exact cost depends on your infrastructure size and compliance requirements. Book a free discovery call to discuss your needs.
Have a question that's not listed here? We're happy to help.
Ask Us AnythingRelated Projects
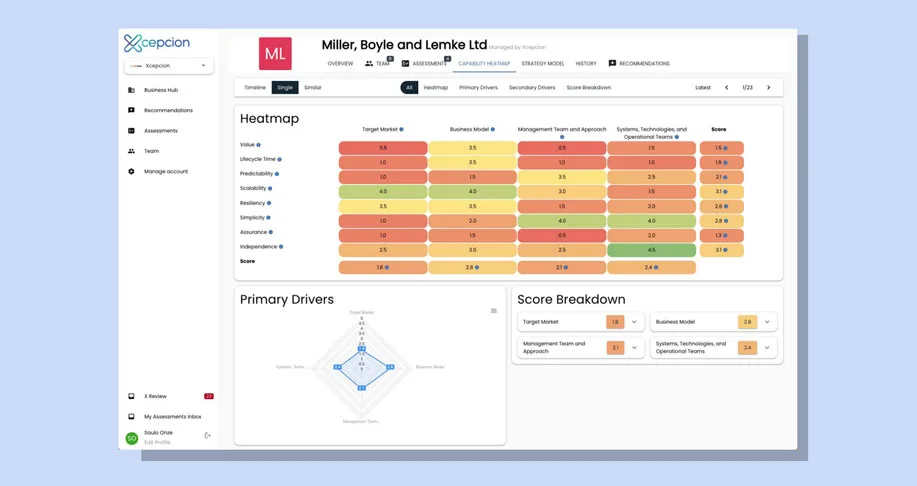
"Working with Nano Solutions was a game-changer for our digital transformation journey. They understood our needs and delivered solutions that truly made a difference."
— Sarah Mitchell, CEO, Xcepcion
Last reviewed: June 2026
Ready to Get Started?
Book a free discovery call to discuss your project. No obligation, no jargon — just a conversation about what you need.